Audit Services
The Internal Audit Office provides a variety of services to the University community. Listed below are some of the services.
Operational Audits
Operational Audit is a systematic process of evaluating an organization's effectiveness, efficiency, and economy of operations under management's control and reporting to appropriate stakeholders the results of the evaluation along with recommendations for improvement.
Compliance Audits
The Internal Audit Office performs compliance audits to provide a comprehensive review of the University’s adherence to regulatory guidelines. Our audit reports evaluate the strength and thoroughness of compliance preparations, security policies, user access controls, and risk management procedures.
In AUC’s Office of General Counsel and Compliance, the focus is on encouraging ethical behavior on campus by educating employees on the AUC’s code of ethics and providing compliance oversight.
Financial Audits
Financial audits address the questions of accounting and reporting of financial transactions, including commitments, authorizations, and receipt and disbursement of funds. The purpose is to verify that there are sufficient controls over cash and cash equivalent assets and that there are adequate process controls over the acquisition and use of resources.
Information Systems (IS) Audits
IT Internal Audit identifies weaknesses or control deficiencies in technology acquisition, implementation, and operation through performing different types of audit, including:
- General IT controls audits
- System development and applications audits
- Technology infrastructure, application systems, and security audits
- Operational/integrated audit
- Investigations
- Administrative audits
- Proactive consulting
- Risk assessments
- Informal awareness training and user education
To provide maximum value to the university, the Internal Audit Office follows the best practices and internationally accepted frameworks as a base for our audit as:
- ISACA (Information Systems Audit and Control Association) and ITGI’s (IT Governance Institute), and COBIT (Control Objectives for Information and Related Technology) by ISACA (Information Systems Audit and Control Association), and ITGI’s (IT Governance Institute)
- ITIL (Information Technology Infrastructure Library)
- ISO 27000 series (The International Organization for Standardization)
- COSO (The Committee of Sponsoring Organizations of the Treadway Commission) and Integrated ERM (Enterprise Risk Management)
The objectives of IT audit include assessment and evaluation of processes that ensure:
- Asset safeguarding, such as data objects in their widest sense, application system, technology, resources to house and support information systems, and staff skills, awareness and productivity
- Ensures that the following seven attributes of data or information are maintained:
- Confidentiality: concerns protection of sensitive information from unauthorized disclosure.
- “Integrity: relates to the accuracy and completeness of information as well as to its validity in accordance with the business' set of values and expectations.
- Availability: relates to information being available when required by the business process, and hence also concerns the safeguarding of resources.
- Effectiveness: deals with information being relevant and pertinent to the business process as well as being delivered in a timely, correct, consistent and usable manner.
- Efficiency: concerns the provision of information through the optimal (most productive and economical) usage of resources.
- Compliance: deals with complying with those laws, regulations and contractual arrangements to which the business process is subject; i.e., externally imposed business criteria. This essentially means that systems need to operate within the ambit of rules, regulations and/or conditions of the organization.
- Reliability of information.
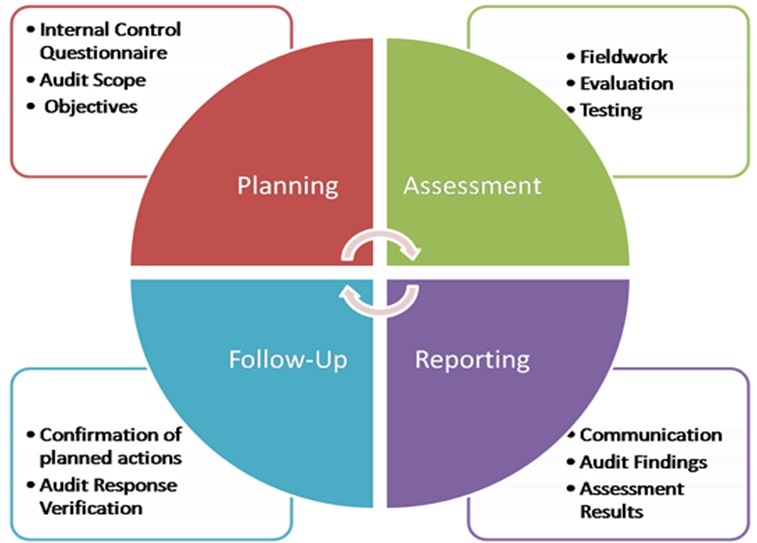
Phases of the Audit Process
The audit process includes the following steps:
Investigative Audits
Investigative Auditing consists of the prevention, detection, and quantification of fraud, money laundering, terror finance, and corruption. Investigative Auditing involves the examination of accounts and the use of accounting procedures to discover financial irregularities and to follow the movement of funds and assets in and out of the University. Fraud, internal theft, use of University’s resources for personal gains, and conflicts of interest are examples of reasons for investigative audits.
The objects of Investigative Auditing include:
- Identification of suspects
- Determination of damages
- Quantification of damages
- Prevention of damage
- Identification of financial activity
- Tracing of financial assets